Acurast raises $11M to turn smartphones into confidential compute nodes
Smartphone-based decentralized confidential compute project Acurast has raised $11 million, claiming tamper-resistant execution on consumer phones and secure hardware verification.
According to a Thursday announcement shared with Cointelegraph, Acurast raised $11 million from Ethereum co-founder and Polkadot founder Gavin Wood, MN Capital founder Michael van de Poppe and GlueNet founder Ogle, among others. The project aims to launch its mainnet on Nov. 17, and plans to release its native token ACU alongside it.
Acurast founder Alessandro De Carli said “billions of smartphones are the most battle-tested hardware on earth” and that the company hopes to reduce costs by leveraging them for “verifiable, confidential compute.”
The network explorer reports that nearly 150,000 phones have already joined the network and processed over 494 million transactions, enabling the deployment of almost 94,200 services.
“We remove the gatekeepers, reduce the costs, and bring secure, trustless computation to anyone, anywhere, and all without a data center,” De Carli claimed.

Related: Decentralized compute networks will democratize global AI access
Confidential compute on third-party hardware?
Acurast says it enables confidential computing — where users with physical access to smartphones running the node software cannot access the data used for computation — to be provided by anyone. This requires a setup that ensures, to a high degree of certainty, that the smartphone’s owner cannot alter the software in a way that compromises this secrecy.
To this end, the project’s developers implemented a series of checks to ensure that the smartphone is running manufacturer-approved software that would not compromise its security assumptions. Still, similar measures have been implemented by banking app developers for many years, only for communities of custom firmware such as Graphene OS to find workarounds that allow them to run the applications on their non-sanctioned setups. De Carli said that this does not apply to Acurast’s app.
De Carli told Cointelegraph that the Acurast processor application sends hardware-backed key pairs with key attestation to the Acurast protocol. If those do not match those provided by the smartphone producer, “the Acurast processor is not able to get a valid attestation, thus cannot participate in the network.”
De Carli said that “this ensures only genuine and attested hardware can be onboarded” and unsuitable environments “cannot be onboarded, because they don’t get the signed attestation attached to their keys,” meaning the phone’s owner cannot tamper with user data or the execution environment.
Related: Dubai moves to regulate machine economy with DePIN peaq network
The security limitations
Still, the security assumption breaks if a manufacturer-endorsed smartphone operating system — iOS or Android — is exploited in the right way by malware or its rightful owner.
De Carli mostly dismissed the notion, saying that “if you manage to find an exploit that allows you to do so, you effectively are eligible for a multimillion-dollar bounty and the exploit would be fixed shortly thereafter” — pointing to Google’s bug bounty program as an example.
Still, in the past, such vulnerabilities were indeed discovered.
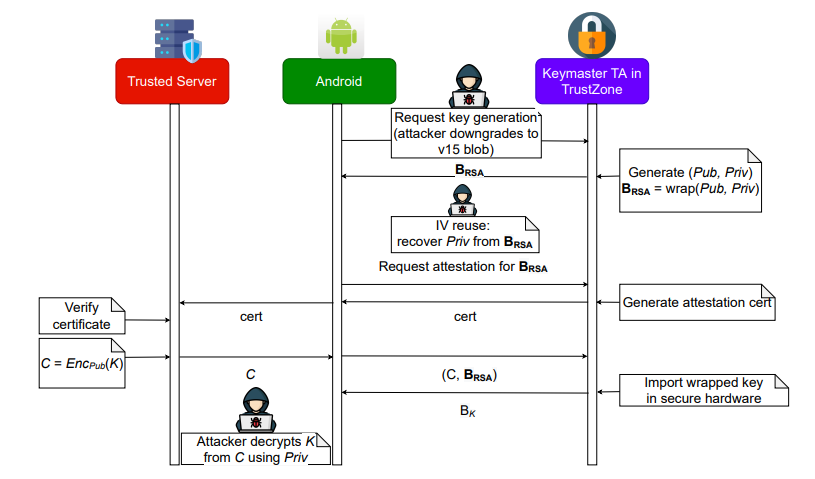
For instance, in Samsung’s TrustZone Operating System, a keymaster AES-GCM IV-reuse attack was discovered in 2022, which allowed protected key extraction and abuse of attestation. Furthermore, an attacker who has already compromised the app process or the kernel will likely be able to encrypt and decrypt content, but won’t be able to extract the private key itself.
Magazine: Blockchain’s next big breakthroughs: What to watch
You may also like
Archives
- May 2026
- April 2026
- March 2026
- February 2026
- January 2026
- December 2025
- November 2025
- October 2025
- September 2025
- August 2025
- July 2025
- June 2025
- May 2025
- April 2025
- March 2025
- February 2025
- January 2025
- December 2024
- November 2024
- October 2024
- September 2024
- January 2024
- December 2023
- January 2023
- December 2022
- January 2022
- December 2021
- January 2021
- December 2020
- December 2019